Tools for Penetration Testing and Simulations: A Comprehensive Guide
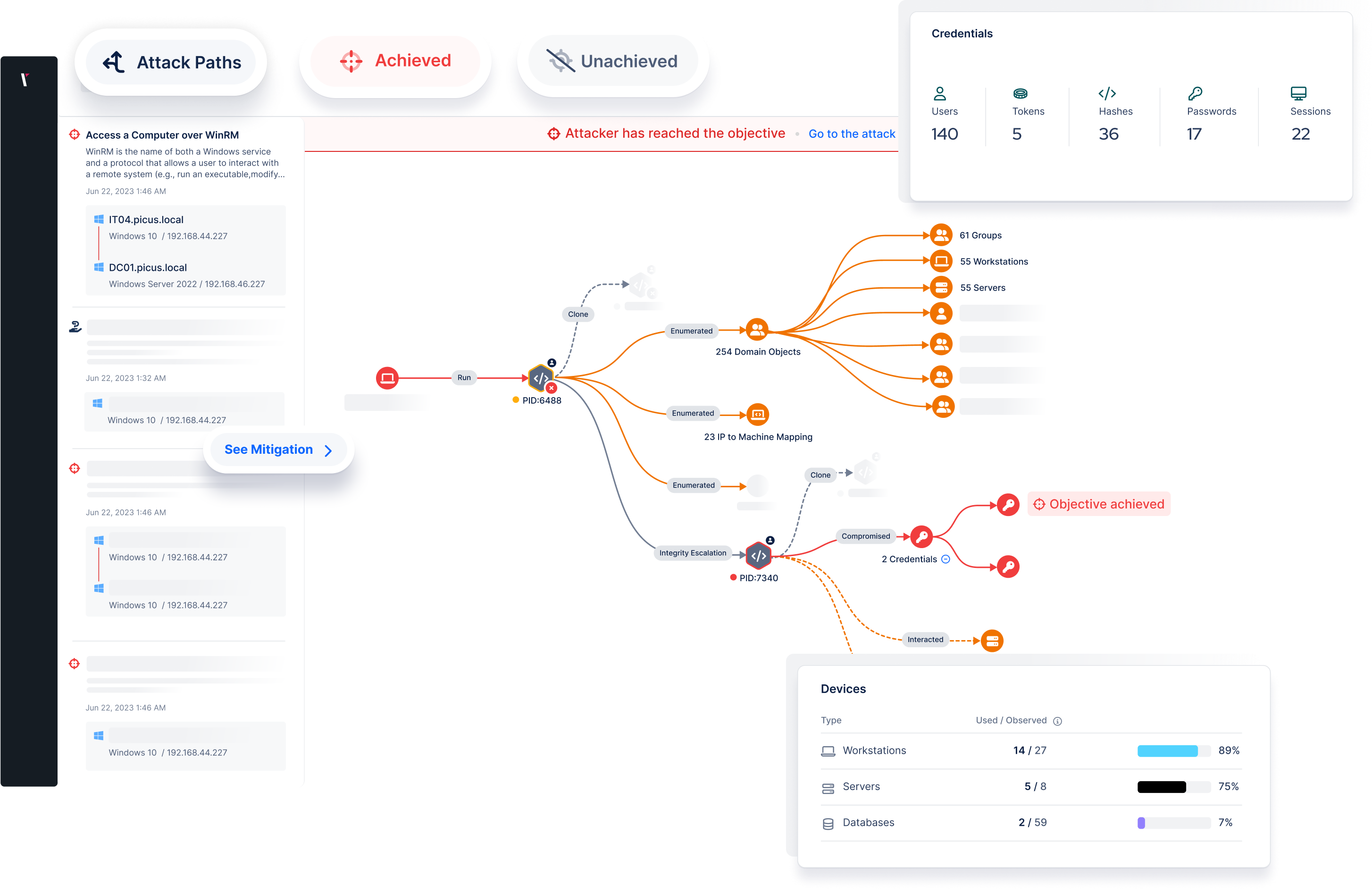
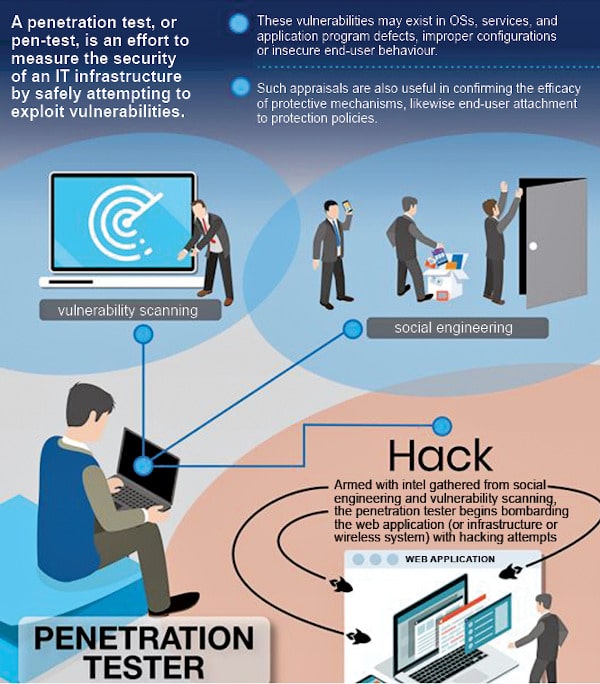
As a security professional, you understand the importance of simulating real-world attacks on your network and systems to identify vulnerabilities and strengthen your defenses. The right tools can make all the difference in the success of your penetration testing and simulations. In this article, we'll explore the top tools for pentesting and simulations, including their features, pricing, and how they can enhance your cybersecurity strategy.
Top Penetration Testing Tools in 2023
- Kali Linux: The gold standard for penetration testing, Kali Linux is a Debian-based Linux distribution designed for digital forensics and penetration testing.
- Metasploit: A widely used penetration testing framework that helps identify system vulnerabilities by providing a comprehensive suite of exploits, payloads, and tools for simulating real-world attacks.
- Empire: An open-source, Python-based post-exploitation framework that allows you to interact with Windows and Linux systems after exploitation.
- Insider: A Windows-based post-exploitation framework that allows you to interact with Windows systems after exploitation.
- Charles Charlie: A man-in-the-middle (MitM) tool that allows you to intercept and modify HTTP/HTTPS traffic.
Such details provide a deeper understanding and appreciation for Tools For Penetration Testing And Simulations.
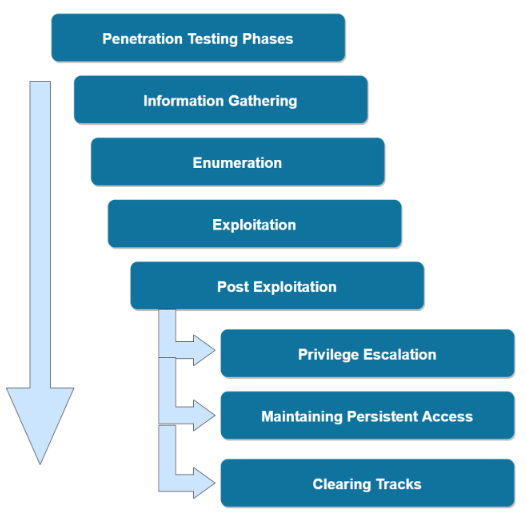
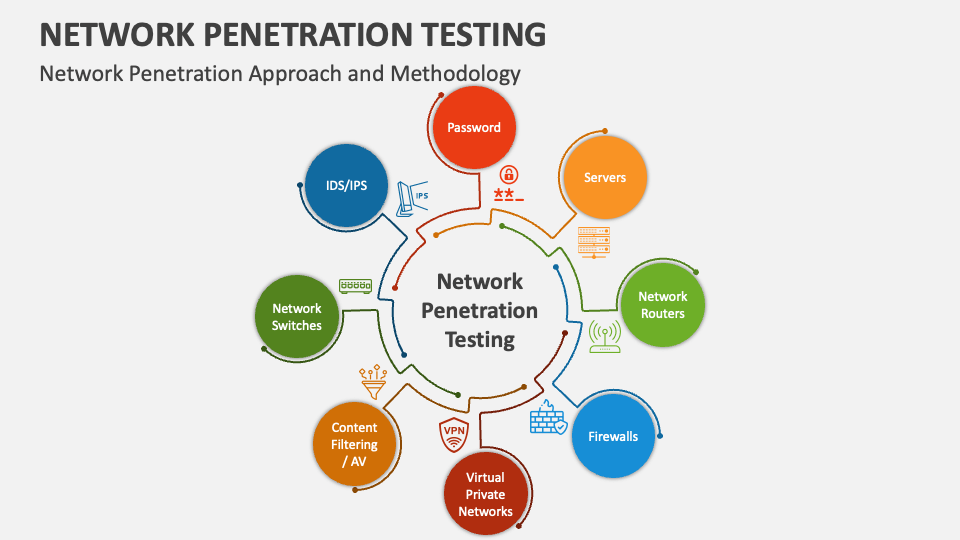
Penetration testing tools simplify and enhance the process of identifying vulnerabilities by automating tasks like scanning networks, finding security gaps, and exploiting vulnerabilities to test defenses. They provide the technical edge required to identify and exploit vulnerabilities with precision.
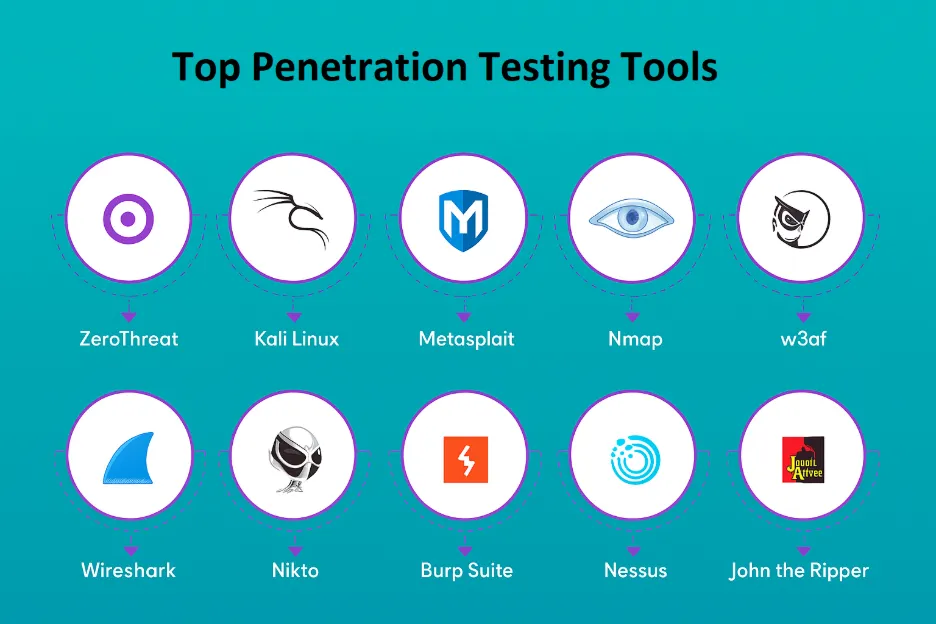
Top 10 Free Penetration Testing Tools
Looking for free penetration testing tools to enhance your cybersecurity strategy and manual review process? Here are the top 10 free tools:
Such details provide a deeper understanding and appreciation for Tools For Penetration Testing And Simulations.
- TryHackMe: A free online platform for learning cybersecurity, using hands-on exercises and labs, all through your browser!
- Nessus: A popular vulnerability scanner that identifies security vulnerabilities in your network, system, and application.
- Nmap: A powerful network scanning tool that helps identify open ports, services, and operating systems.
- Wireshark: A free and open-source network protocol analyzer that helps troubleshoot network issues.
- SQLMap: A powerful tool for detecting SQL injection vulnerabilities in web applications.
- OWASP ZAP: A free, open-source web application security scanner that helps identify vulnerabilities in web applications.
- Burp Suite: A comprehensive web application security testing tool that helps identify vulnerabilities in web applications.
- CovertScanner: A stealthy, low-profile vulnerability scanner that helps identify unknown vulnerabilities.
- Masscan: A fast, lightweight network scanning tool that helps identify open ports and services.
- MassProxy: A tool that generates a large number of HTTP proxy servers to help evade detection.
Free Penetration Testing Tools for Vulnerability Scanning
- Try ZeroThreat: A free pentesting tool that scans web apps & APIs for vulnerabilities, automates threat detection, and improves security posture.
- AWS Inspector: A cloud-based security tool that helps identify security vulnerabilities and misconfigurations in your AWS resources.
- Google Cloud Security Command Center: A cloud-based security tool that helps identify security vulnerabilities and misconfigurations in your Google Cloud resources.
- Microsoft Azure Security Center: A cloud-based security tool that helps identify security vulnerabilities and misconfigurations in your Azure resources.
- Azure Security Center for Compute: A cloud-based security tool that helps identify security vulnerabilities and misconfigurations in your Azure resources.
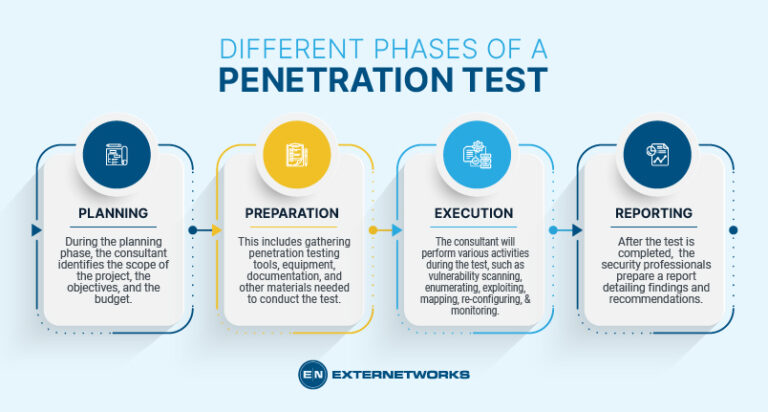
Furthermore, visual representations like the one above help us fully grasp the concept of Tools For Penetration Testing And Simulations.
Penetration Testing and Simulations: A Comprehensive Guide
Penetration testing and simulations are critical components of a comprehensive cybersecurity strategy. By using the right tools, you can simulate real-world attacks on your network and systems, identify vulnerabilities, and strengthen your defenses.
Want to know the top 25 safety tips for penetration testing? Here are some essential tips to help you perform successful pen tests:
- Always obtain explicit consent from the target system owner.
- Use a permission slip or contract before performing a pen test.
- Prepare a detailed test plan and procedure.
- Engage a skilled team of testers.
- Use realistic tools and techniques.
- Focus on a specific scope and objective.
- Test for weaknesses, not for compliance.
- Keep the target system owner informed.
- Debrief the target system owner after the test.
- Include audit controls to prevent unauthorized access.
- Network with other pen testers to learn and improve.
- Regularly update your testing tools and techniques.
- Practically test any vulnerability you report.
- Prioritize the threat profile.
- Speech supported.
- Educate users about potential vulnerabilities.
- Ideally cannot decrypt info after testing.
- Network Admin should be trained.
- Expressly accounting it.
- Debrief, brief, summarize.
- Content analysis likely conclude PTSDN banking wells that bank inmate's logs mint....
By following these safety tips and using the right tools for penetration testing and simulations, you can enhance your cybersecurity strategy, identify vulnerabilities, and strengthen your defenses.















-1478x986.png)
![Best Penetration Testing Tools in 2026 [Paid & Open Source] Best Penetration Testing Tools in 2026 [Paid & Open Source] - Tools For Penetration Testing And Simulations](https://qualysec.com/wp-content/uploads/2025/01/Penetration-Testing-Tools_qualysec-768x432.png)