Wireless G Network Setup for Secure Data Centers: A Comprehensive Guide
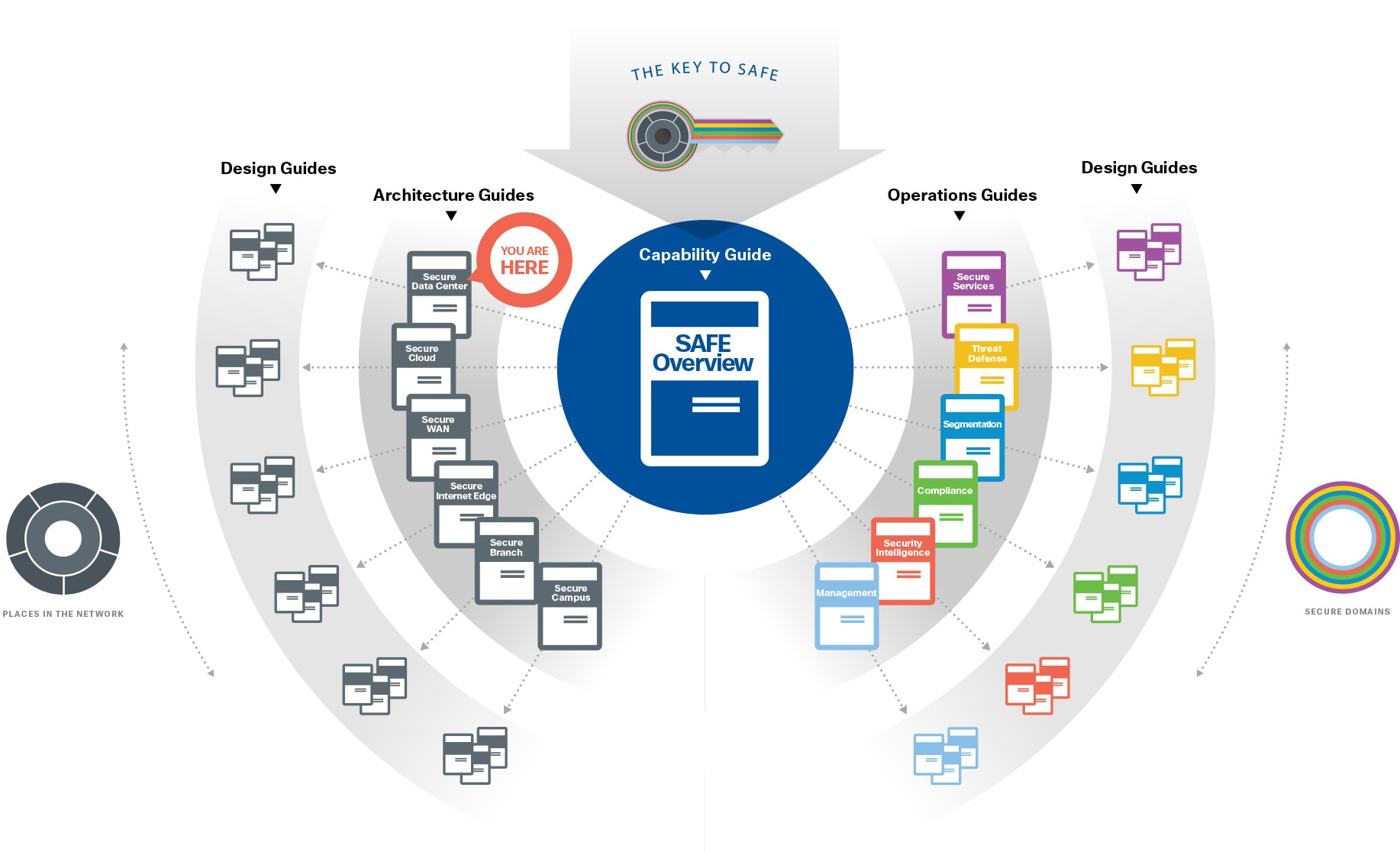
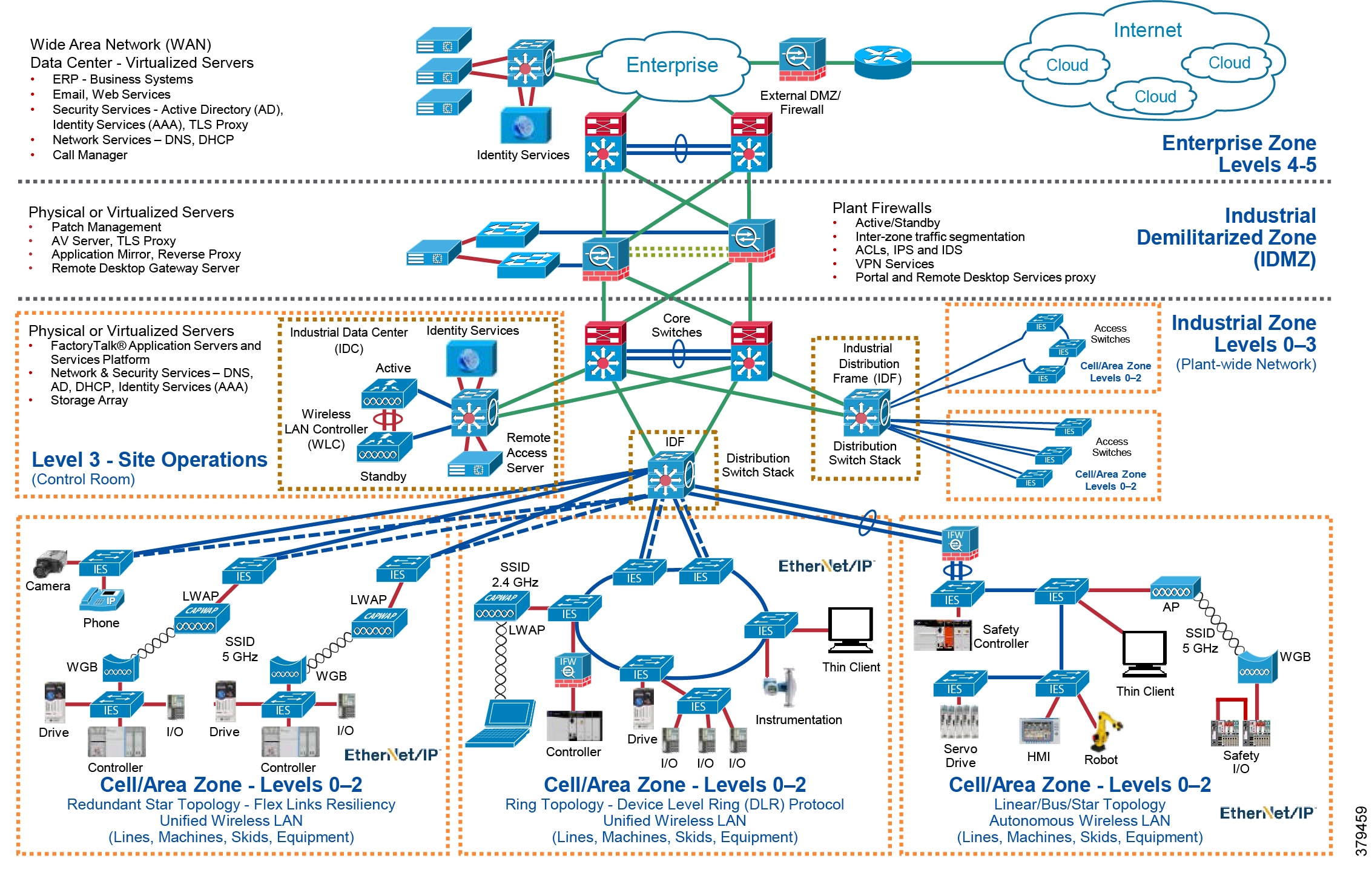
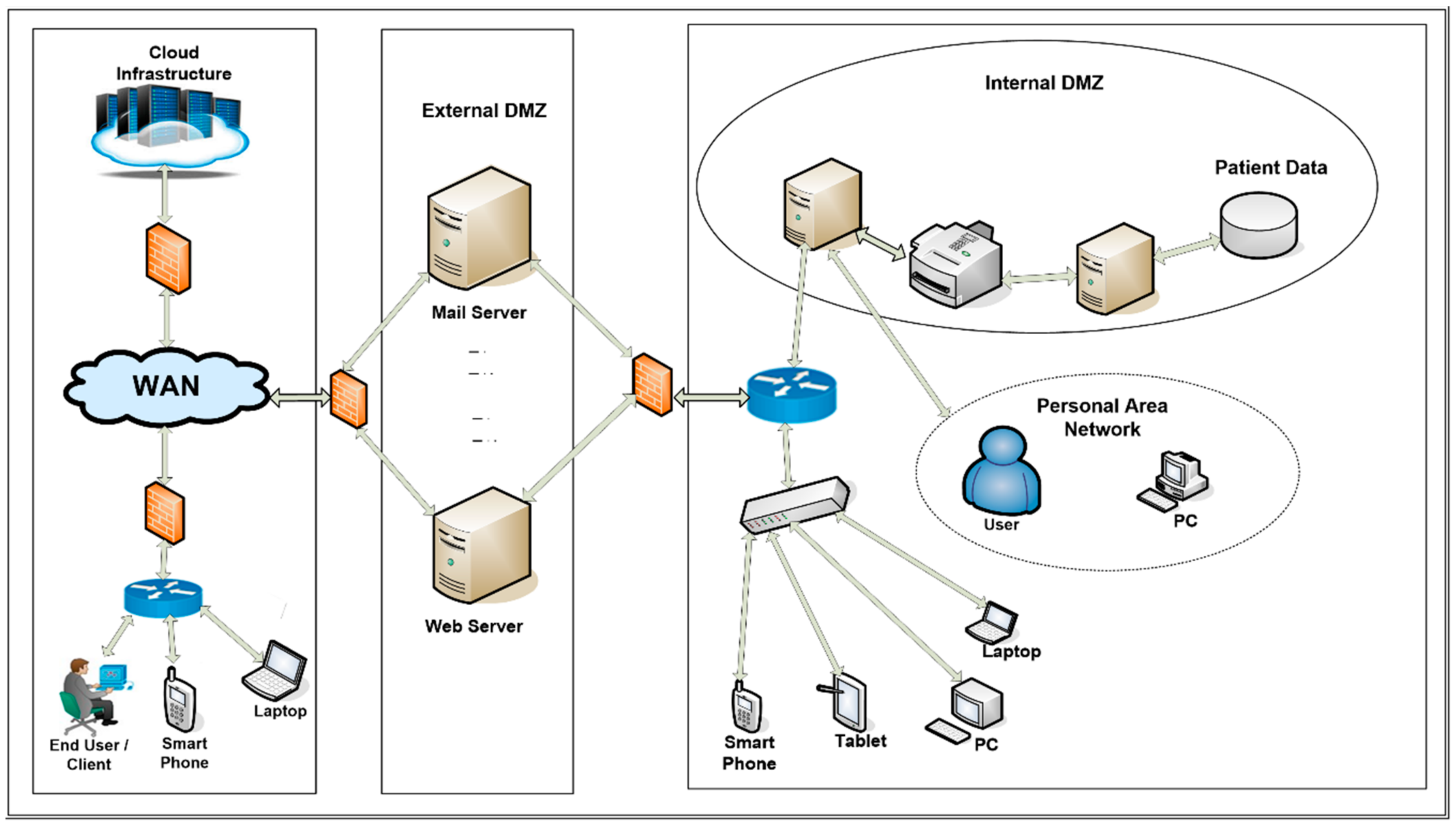
In today's digital landscape, wireless connectivity plays a crucial role in ensuring seamless access to networks and data. As a result, setting up and securing wireless networks is essential for protecting company data, preventing unauthorized access, and complying with cybersecurity best practices. In this article, we will explore the best practices for Wi-Fi configuration and network encryption to safeguard your IT infrastructure. The Secure Data Center is a place where a company centralizes data and performs services for business. Data centers contain hundreds to thousands of physical and virtual servers that are segmented by applications, zones, and other methods. According to a recent report, most data centers are exposed to a vast array of threats, including physical attacks, hacking, and supply chain attacks.Wireless Network Security for Data Centers: Best Practices
- Implement WPA2/AES (Advanced Encryption Standard) encryption**: The most widely used encryption standard, WPA2/AES, is the minimum requirement for securing your wireless network. Make sure to enable WPA2/AES encryption on both the router and client devices.
- Configure Strong Passwords and Authentication**: Use strong, unique passwords and multi-factor authentication (MFA) to prevent unauthorized access to your network and data.
- Restrict Network Access**: Limit network access to authorized personnel only. Implement role-based access control (RBAC) to ensure that users have the minimum amount of access required for their job functions.
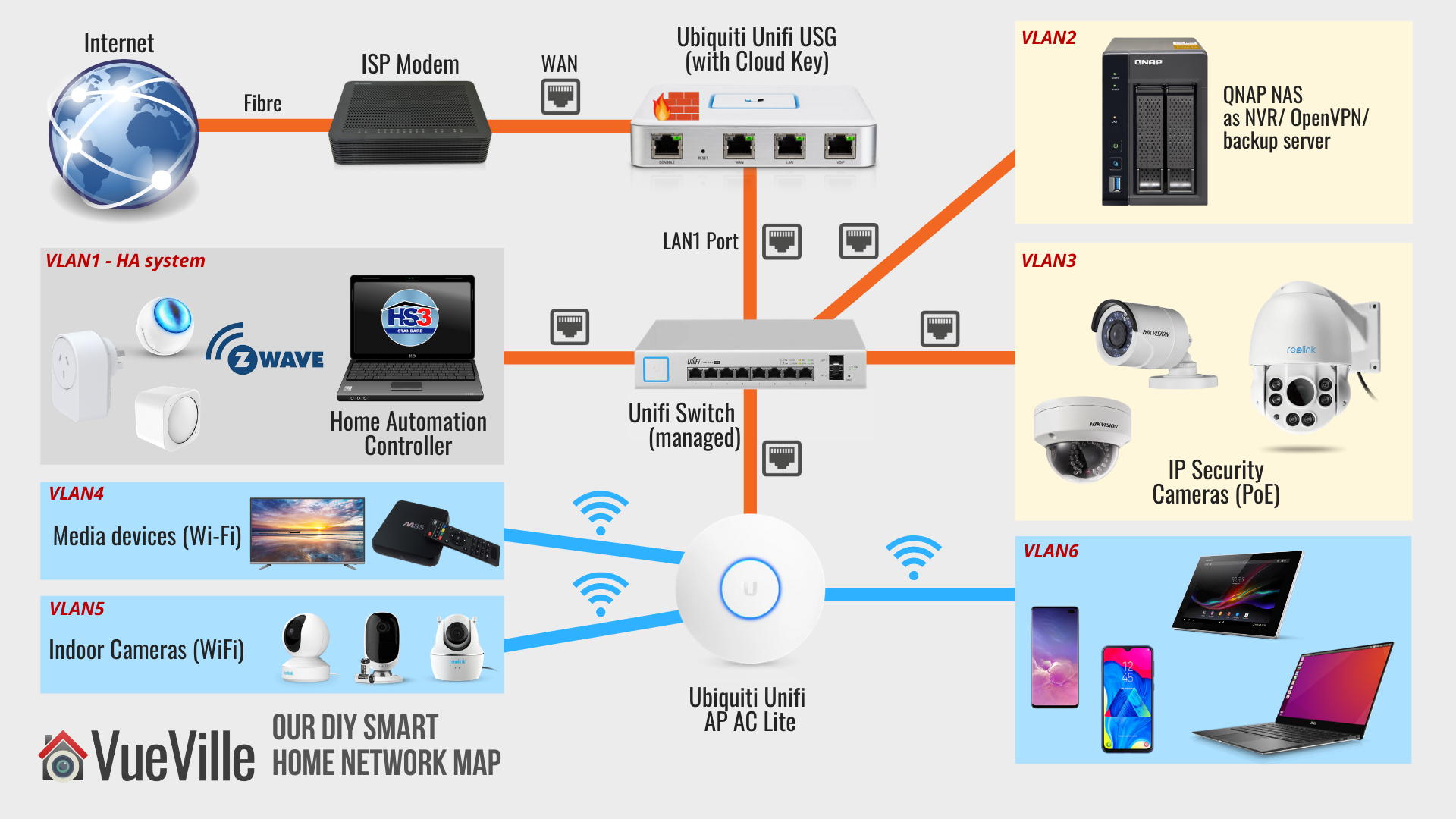
- Implement Guest Network**: Set up a separate guest network for visitors and contractors to reduce the risk of insecure connections to your primary network.
- Regularly Update Firmware and Software**: Regularly update your router's firmware and software to ensure you have the latest security patches and features.
- Maintain Network Segmentation**:
- Conduct Regular Network Security Audits**: Regular security audits and vulnerability scanning will help identify potential security risks and threats.
- Implement Intrusion Detection and Prevention Systems**: Monitoring for suspicious activity, detect and stop potential attacks and malware from occurring.

Wireless G Network Setup for Secure Data Centers: Equipment Considerations

- Wireless Router**: Choose a wireless router that supports WPA2/AES encryption, has a gigabit Ethernet port, and a USB port for firmware upgrades and guest access.
- Access Points (APs)**: Use high-gain antennas to increase coverage and throughput. Consider directional antennas to focus the signal towards users.
- Wireless Network Cards**: Make sure your network cards support 802.11ac or 802.11ax (Wi-Fi 6) standards for fast and efficient connections.
Wireless G Network Setup for Secure Data Centers: Tips and Considerations
Some additional tips and considerations for setting up a secure wireless network for your data center include:- Position Access Points Strategically**: Place APs in a central location to minimize dead zones and maximize coverage.
- Use Quality of Service (QoS)**: Set bandwidth prioritization and allocation to ensure critical applications get the required priority and bandwidth.
- Optimize Channel Width**: Use the optimal channel width for the type of data being transmitted to reduce interference and improve performance.