Database Security Protocols to Prevent Hacking
The Importance of Database Security Protocols
Database security protocols refer to the measures used to protect a database management system from malicious threats and unauthorized access. This includes ensuring that only authorized personnel have access to sensitive data, maintaining data accuracy and availability, and securing the database against cyber attacks.

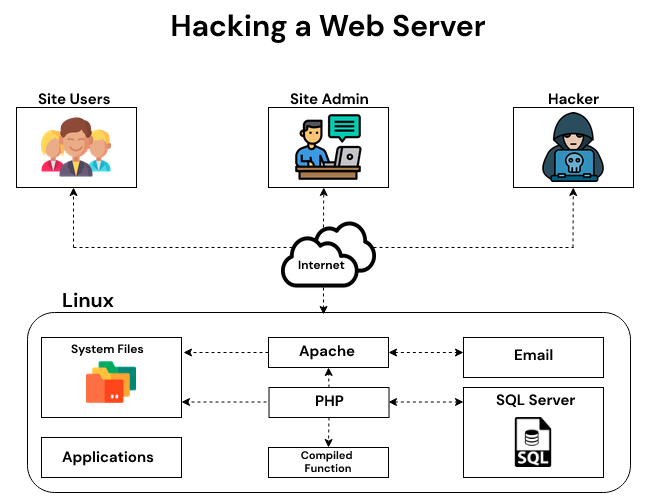
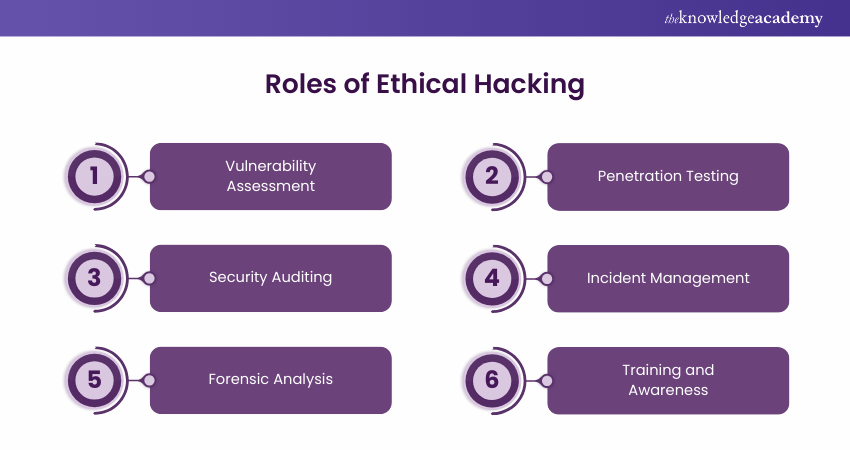
Furthermore, visual representations like the one above help us fully grasp the concept of Database Security Protocols To Prevent Hacking.
Top 10 Database Security Protocols to Prevent Hacking
- 1. Continuous Monitoring: Regularly monitoring database activity can help identify and detect security threats in real-time.
- 2. Network Segmentation: Segmenting your network into smaller, isolated areas can help prevent the spread of malware and limit access to sensitive data.
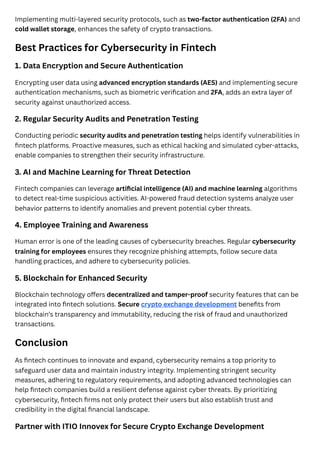
- 3. Robust Encryption: Encrypting all database connections using the Transport Layer Security (TLS) protocol and encrypting disk storage can protect data in transit and prevent data loss or theft.
- 4. Access Controls: Implementing strict access controls can ensure that only authorized personnel have access to sensitive data and prevent unauthorized access.
- 5. Regular Security Audits: Conducting regular security audits can help identify vulnerabilities and weaknesses in your database security protocols.
- 6. Secure Password Management: Implementing secure password management practices can prevent unauthorized access to sensitive data.
- 7. Database Backup: Regularly backing up your database can help prevent data loss in the event of a cyber attack or system failure.
- 8. Secure Coding Practices: Implementing secure coding practices, such as input validation and error handling, can help prevent common web application vulnerabilities.
- 9. Secure Data Storage: Implementing secure data storage practices, such as storing sensitive data in encrypted form, can help prevent data breaches.
- 10. Incident Response Planning: Developing an incident response plan can help ensure that you are prepared to respond to a cyber attack and minimize the damage.

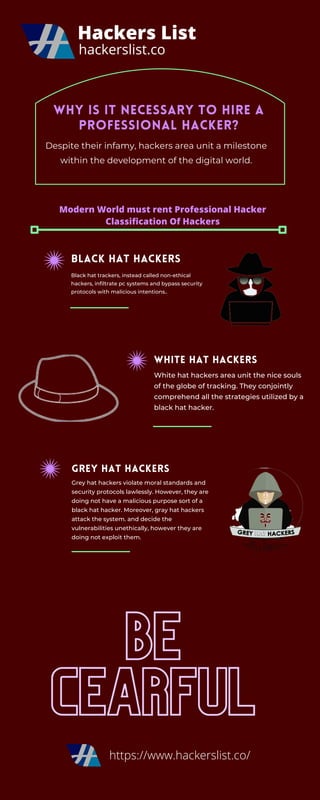
This particular example perfectly highlights why Database Security Protocols To Prevent Hacking is so captivating.
Best Practices for Database Security
In addition to the database security protocols outlined above, there are several best practices that can help prevent hacking of your critical data assets. These include:

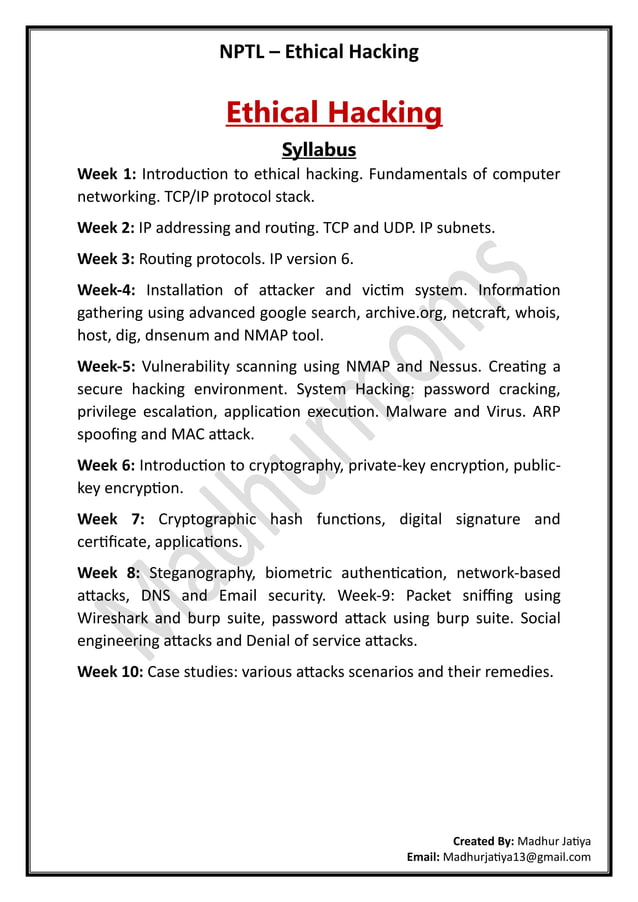
Furthermore, visual representations like the one above help us fully grasp the concept of Database Security Protocols To Prevent Hacking.
- Implementing a layered security methodology: Using multiple security capabilities targeted at different security scopes can provide a defense-in-depth solution.
- Conducting regular security training: Providing regular security training to personnel can help ensure that they are aware of the importance of database security and can identify potential security threats.
- Implementing a security information and event management (SIEM) system: A SIEM system can provide real-time monitoring and analysis of security-related data from various sources.
- Conducting regular security assessments: Conducting regular security assessments can help identify vulnerabilities and weaknesses in your database security protocols.
Conclusion
Protecting your critical data assets from cyber threats requires a robust database security strategy that includes a combination of best practices and security protocols. By implementing the database security protocols outlined above and following the best practices outlined in this article, you can help prevent hacking and ensure the security and integrity of your sensitive data.
Remember, database security is a continuous process that requires regular monitoring, assessment, and improvement. By staying one step ahead of cyber threats, you can help ensure the security and integrity of your sensitive data and protect your business from the financial and reputational damage caused by a data breach.